- Cisco AnyConnect Secure VPN Adapter has DNS servers set to DC1/DC2. Internet is functional because DNS fails over to DNS entries in LAN adapters. Here is debug logging on the DNS server for two workstations. Domain.com.au is the AD domain. 1/ 192.168.3.111 = VPN Client 2/ 192.168.0.100 = LAN Client.
- Within this same location, we will add the AnyConnect profile. Select “Add AnyConnect File” at the top-right once again. Enter a name, browse to the profile, select AnyConnect Client Profile from as the File Type and select “Save” when complete. This xml profile can be created using the Cisco VPN Profile Editor tool on a Windows machine.
Sep 16, 2019 When the AnyConnect client for macOS attempts to create an SSL connection to a gateway running IOS, or when the AnyConnect client attempts to create an IPsec connection to an ASA from behind certain types of routers (such as the Cisco Virtual Office (CVO) router), some web traffic may pass through the connection while other traffic drops. We have a Cisco ASA device and we are using the Cisco AnyConnect VPN client. My issue is that when users connect with the AnyConnect Client they have no DNS server assigned and can only access internal network resources by IP.
Introduction
This document describes how to configure the Cisco AnyConnect Secure Mobility Client for Dynamic Split Exclude Tunneling via the Cisco Adaptive Security Device Manager (ASDM) on a Cisco Adaptive Security Appliance (ASA).
Prerequisites
Requirements
Cisco Anyconnect Dns Issue
Cisco recommends that you have knowledge of these topics:
- Basic knowledge of ASA.
- Basic knowledge of Cisco Anyconnect Security Mobility Client.
Components Used
The information in this document is based on these software versions:
- ASA 9.12(3)9
- ASDM 7.13(1)
- AnyConnect 4.7.0
The information in this document was created from the devices in a specific lab environment. If your network is live, make sure that you understand the potential impact of any command.
Background Information
Anyconnect Split tunneling allows Cisco AnyConnect Secure Mobility Client secure access to corporate resources via IKEV2 or Secure Sockets Layer (SSL). Prior to AnyConnect version 4.5, based on the policy configured on Adaptive Security Appliance (ASA), Split tunnel behavior could be Tunnel Specified, Tunnel All or Exclude Specified.
With the advent of cloud-hosted computer resources, services may resolve to a different IP address based on the location of the user or based on the load of the cloud-hosted resources. Since Anyconnect Secure Mobility Client provides split-tunneling to static subnet range, host or pool of IPV4 or IPV6, it becomes difficult for Network Administrators to exclude domains/FQDNs while configuring AnyConnect. For example, a Network Administrator might want to exclude the Cisco.com domain from Split tunnel configuration but the DNS mapping for Cisco.com might change since it is cloud-hosted.
Using Dynamic Split Exclude tunneling, Anyconnect dynamically resolves the IPv4/IPv6 address of the hosted application and makes necessary changes in the routing table and filters to allow the connection to be made outside the tunnel.
Starting with AnyConnect 4.5, Dynamic Spit Tunnelling can be used wherein Anyconnect dynamically resolves the IPv4/IPv6 address of the hosted application and makes necessary changes in the routing table and filters to allow the connection to be made outside the tunnel
Configuration
This section describes how to configure the Cisco AnyConnect Secure Mobility Client on the ASA.
Network Diagram
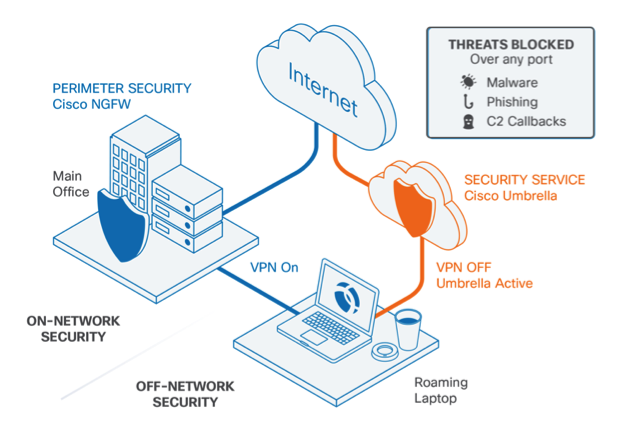
This image shows the topology that is used for the examples of this document.
Step 1. Create AnyConnect Custom Attributes.
Navigate to Configuration > Remote Access VPN > Network (Client) Access > Advanced > AnyConnect Custom Attributes. click Add button, and set dynamic-split-exclude-domains attribute and optional description, as shown in the image:
Step 2. Create AnyConnect Custom Name and Configure Values.
Navigate to Configuration > Remote Access VPN > Network (Client) Access > Advanced > AnyConnect Custom Attribute Names. click Add button, and set the dynamic-split-exclude-domains attribute created earlier from Type, an arbitrary name and Values, as shown in the image:
Be careful not to enter a space in Name. (Example: Possible 'cisco-site' Impossible 'cisco site') When multiple domains or FQDNs in Values are registered, separate them with a comma (,).
Step 3. Add Type and Name to the Group Policy.
Navigate to Configuration> Remote Access VPN> Network (Client) Access> Group Policies and Select a Group Policy. Thereafter, navigate to Advanced> AnyConnect Client> Custom Attributes and add the configured Type and Name, as shown in the image:
CLI Configuration Example
Cisco Anyconnect Dns Configuration
This section provides the CLI configuration of Dynamic Split Tunneling for reference purposes.
Limitations
- ASA version 9.0 or later is needed to use Dynamic Split Tunneling custom attributes.
- Wildcard in the Values field is not supported.
- Dynamic Split Tunneling is not supported on iOS (Apple) devices (Enhancement Request: CSCvr54798).
Verify
In order to verify configured Dynamic Tunnel Exclusions, Launch AnyConnect software on the client, click Advanced Window > Statistics, as shown the image:
You can also navigate to Advanced Window > Route Details tab wherein you can verify Dynamic Tunnel Exclusions are listed under Non-Secured Routes, as shown in the image.
In this example, you have configured www.cisco.com under Dynamic Tunnel Exclusion list and the Wireshark capture collected on the AnyConnect client's physical interface confirms that the traffic to www.cisco.com (173.37.145.84), is not encrypted by DTLS.
Troubleshoot
In Case the Wildcard is Used in Values Field
If a wildcard is configured in Values field, for example, *.cisco.com is configured in Values, AnyConnect session is disconnected, as shown in the logs:
Note: As an alternative, you can use the cisco.com domain in Values for allowing FQDNs such as www.cisco.com and tools.cisco.com.
In Case Non-Secured Routes is not seen in Route Details Tab
AnyConnect client automatically learns and adds the IP address and FQDN in the Route Details tab, when the client initiates the traffic for the excluded destinations.
In order to verify that the AnyConnect users are assigned to the correct Anyconnect group-policy, you can run the command 'show vpn-sessiondb anyconnect filter name <username>'
General Troubleshoot
Cisco Anyconnect For Mac
You can use the AnyConnect Diagnostics and Reporting Tool (DART) in order to collect the data that is useful for troubleshooting AnyConnect installation and connection problems. The DART Wizard is used on the computer that runs AnyConnect. The DART assembles the logs, status, and diagnostic information for the Cisco Technical Assistance Center (TAC) analysis and does not require administrator privileges to run on the client machine.
Related Information
- ASDM Book 3: Cisco ASA Series VPN ASDM Configuration Guide, 7.13 - Configure Dynamic Split Tunneling
